NordVPN To Retire Meshnet in December 2025
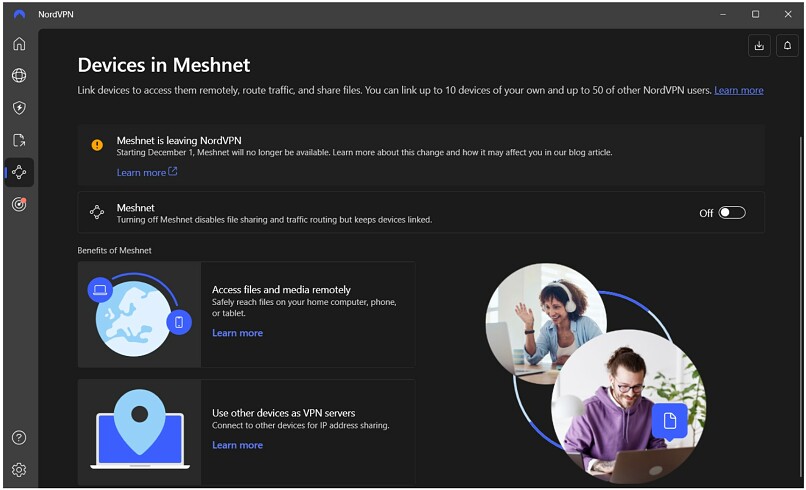
NordVPN announced that it will discontinue its Meshnet feature, effective 1 December 2025. Current and new users will be able to continue using the feature as normal until then. No other features will be impacted by Meshnet’s removal.
NordVPN first unveiled Meshnet in 2022 as a free feature that came installed by default and is currently supported on all its apps, including Windows, macOS, Linux, Android, and iOS. It provided a secure way for users to primarily share files between their devices using a secure connection, no matter where they are.
Users could access the feature simply by installing NordVPN apps, linking the devices, setting permissions, and then sharing files directly from the device’s file explorer. In its official announcement, NordVPN recommends that users start to “plan ahead” and look “into alternative solutions.”
Additionally, they suggest their NordLocker service as a possible replacement. NordLocker is a freemium cloud storage and file-sharing service that offers a 3GB free-forever plan. It’s supported on Chrome, Firefox, Edge, Safari, Android, and iOS, so that users can upload, access, and manage files across all their devices.
NordVPN said that they originally “built it as an extension of our mission to provide safer access to the internet,” but that it failed to reach a “wide enough audience.” Furthermore, NordVPN says that supporting and developing Meshnet requires too many ongoing resources, which it will now redirect to its core VPN capabilities.
NordVPN rolled out post-quantum encryption to all its apps earlier this year. It also launched a new protocol called NordWhisper aimed at bypassing various network blocks. Both these changes also signal a pivot toward the most important functionalities for most VPN users: protecting their data and avoiding internet restrictions.



Please, comment on how to improve this article. Your feedback matters!